How to Tell If Your Router Has Been Hacked in 2026
Your router is the most important device on your home network — and one of the most commonly attacked. In March , the DoJ and Europol dismantled a botnet made up of 360,000 infected routers and IoT devices that had been running undetected for 16 years across 163 countries. Most of those homeowners had no idea their router was compromised. If your router has been hacked, your internet traffic, passwords, and connected devices are all at risk. This guide shows you exactly how to detect a compromised router and what to do about it.
Signs Your Router Has Been Hacked
The most common symptoms of a router that has been hacked are subtle — that’s by design. Attackers don’t want you to notice. Here’s what to look for.
Unexplained slowdowns and latency spikes. If your internet suddenly feels sluggish at odd hours — especially late at night — your router may be participating in a botnet, proxying traffic for someone else, or mining cryptocurrency using your connection. Run a speed test and compare results at different times of day.
Unknown devices on your network. Log into your router’s admin panel and check the connected devices list. If you see devices you don’t recognize — especially ones with generic names or unfamiliar MAC addresses — that’s a serious warning sign. Legitimate smart home devices should all be accounted for.
DNS settings changed without your input. This is one of the most dangerous hacks. Attackers change your router’s DNS servers to ones they control, redirecting your web traffic through their servers to steal credentials. Go to your router’s WAN or Internet settings and verify the DNS servers. They should match what your ISP provides, or your preferred public DNS like 1.1.1.1 (Cloudflare) or 8.8.8.8 (Google) — not anything unfamiliar.
Admin password no longer works. If you’re locked out of your own router admin panel, an attacker may have changed the password after gaining access. This is a clear sign your router has been hacked.
Unexpected firmware version or settings changes. Log into your router and check the firmware version and configuration. Compare to what you had set. If settings have changed — port forwarding rules appeared, remote management was enabled, or the firmware is different — investigate immediately.
Your ISP contacts you about suspicious activity. Some ISPs monitor for unusual traffic patterns and will notify customers if their router is part of a botnet or sending spam. Take these notices seriously.
How Routers Get Compromised
Understanding how your router has been hacked helps you prevent it from happening again.
Default credentials. The single most common attack vector. If you never changed the admin username and password from the factory defaults (admin/admin, admin/password, etc.), an attacker on your network or using automated scanning tools can gain full access in seconds. Default credential databases are freely available online.
Unpatched firmware vulnerabilities. Router firmware contains bugs. Manufacturers release patches, but most home routers run outdated firmware for years because owners don’t update them. The SocksEscort botnet that ran for 16 years exploited exactly this — devices running firmware with known vulnerabilities that never got patched.
Remote management enabled. Many routers have a remote management feature that lets you access the admin panel from the internet. Unless you specifically need this, it should be disabled. When enabled, it exposes your router’s login page to the entire internet.
UPnP exploits. Universal Plug and Play lets devices on your network open ports automatically. While convenient, UPnP has a history of severe vulnerabilities. Disable it if you don’t need it.
Weak WiFi passwords. A weak WPA2 or WPA3 password can be cracked, giving an attacker local network access and from there, access to your router’s admin panel.
Phishing for router credentials. Some attacks work by getting you to click a malicious link while connected to your home network, which then attempts to access your router using default or common credentials from your browser.
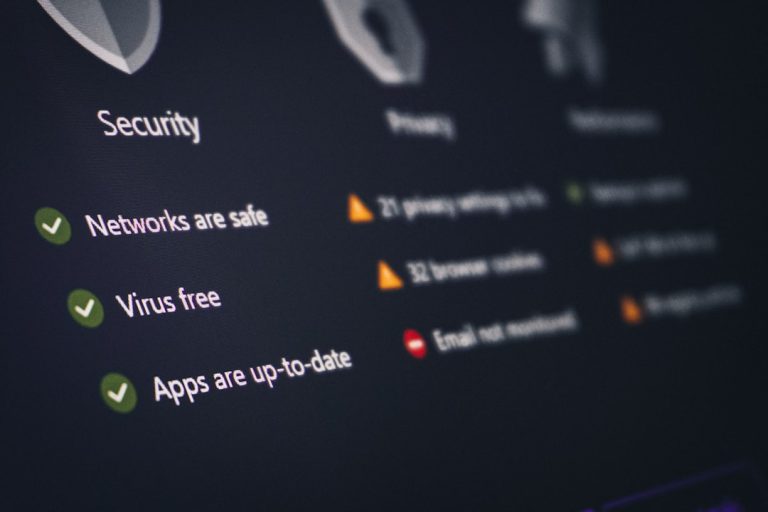
How to Check If Your Router Has Been Hacked
Here’s a systematic checklist:
Step 1: Check your router’s DNS settings. Log into your admin panel (usually 192.168.1.1 or 192.168.0.1). Find the WAN or Internet settings. Look for Primary and Secondary DNS. They should match what your ISP assigned via DHCP, or a DNS provider you chose. If you see 8.8.8.8 and 8.8.4.4 but you never set those, that’s suspicious in context. If you see unknown IPs like 77.x.x.x or 91.x.x.x — those are red flags.
Step 2: Review connected devices. Most routers have a DHCP client list or connected devices page. Write down every device and verify it belongs to you. Look up unfamiliar MAC address prefixes on a MAC lookup tool to identify the manufacturer.
Step 3: Check for open ports and unexpected port forwarding rules. In your router’s firewall or port forwarding section, verify every rule. You should recognize every entry. Unknown port forwarding rules — especially ones pointing to IP addresses inside your network — could indicate an attacker has set up a backdoor.
Step 4: Run a router vulnerability scan. Tools like RouterSecurity.org have free checklists, and Shodan (with a paid account) can show whether your router’s admin interface is visible from the internet.
Step 5: Check your router manufacturer’s website for firmware updates. Compare the firmware version running on your device to the latest available. If you’re multiple versions behind, there may be known vulnerabilities already being exploited in the wild.
What to Do If Your Router Has Been Hacked
Act immediately. Don’t wait.
1. Disconnect compromised devices. If you suspect active compromise, disconnect the router from the internet. This stops any active data exfiltration or botnet participation.
2. Factory reset your router. A hard reset (typically a physical button held for 10-30 seconds) wipes all configuration and returns it to factory defaults. This removes any malicious firmware changes, backdoor accounts, or altered DNS settings.
3. Update firmware before reconnecting. Before bringing the router back online, connect it to a laptop via Ethernet only and check for firmware updates through the admin panel. Install the latest version.
4. Change all credentials. Set a strong, unique admin password (12+ characters, mixed). Change your WiFi password. If you use the same passwords elsewhere, change those too.
5. Disable remote management and UPnP. Turn off any features that expose your router to the internet unnecessarily.
6. Change passwords for all accounts you used on that network. Banking, email, streaming services — assume credentials entered on a compromised network may have been intercepted.
7. Consider replacing the router. If your router is more than 4-5 years old and the manufacturer no longer provides firmware updates, a factory reset only gets you so far. An unsupported router will be vulnerable again. It’s time for a new one.
How to Harden Your Router Against Future Attacks
Once you’ve cleaned up, lock things down properly.
Change the default admin credentials immediately. Use a password manager to generate and store a strong, unique password. Never use the default.
Keep firmware updated. Set a calendar reminder to check for firmware updates quarterly. Better yet, choose a router brand with automatic update support. ASUS, TP-Link, and Netgear all offer auto-update options on modern models.
Disable remote management unless you need it. If you do need remote access to your router, use a VPN instead.
Use WPA3 for your WiFi networks. WPA3 is significantly harder to crack than WPA2. Most routers from 2020 onward support it.
Segment your network. Put IoT devices — smart plugs, cameras, thermostats — on a separate VLAN or guest network so a compromised smart bulb can’t pivot to your NAS or laptop. Our guide to setting up a VLAN for IoT devices covers this step by step.
Choose a router with a strong security track record. Some routers get regular security updates for 5+ years; others are abandoned after 12 months. This matters more than raw speed specs. The CISA home network security guide is a useful reference for building a complete hardening checklist.
The Best Routers with Strong Security Track Records in
If you need to replace a compromised or aging router, prioritize long-term firmware support and built-in security features.
ASUS RT-BE88U — ASUS has one of the best firmware update track records in the consumer space. The RT-BE88U supports Wi-Fi 7, has ASUS AiProtect powered by Trend Micro for network threat detection, and receives regular security patches. Check price on Amazon.
GL.iNet Flint 3 — If you want full control over your router’s security, GL.iNet devices run OpenWrt, giving you access to enterprise-grade security tools, Wireguard VPN, and Adguard Home built in. Ideal for users who want to know exactly what their router is doing. Check price on Amazon.
For a deeper look at top-rated options, see our full best WiFi routers 2026 guide.
The Bigger Picture: IoT Devices Are the Weakest Link
The 360,000-device botnet the DoJ took down in wasn’t just made up of routers — it included thousands of IoT devices too. Security cameras, smart plugs, baby monitors, and network storage devices are all potential entry points if they run outdated firmware and use default credentials.
Apply the same hardening checklist to every device on your network: change default passwords, update firmware, and if a device hasn’t received a security update in over a year, consider replacing it. For smart home security devices specifically, check out our guide to best home security cameras in for models with strong security track records.
Summary
If your router has been hacked, the consequences can range from slow internet to full credential theft. The good news is that the fix is simple: factory reset, update firmware, harden credentials, and segment your network. Most compromised routers get that way because of default passwords and years of unpatched firmware — both completely preventable.
The biggest thing you can do right now, today, is log into your router admin panel and check your DNS settings, connected devices, and firmware version. It takes five minutes and could save you months of headaches.
Recommended Router Upgrade
If your router has been compromised and is end-of-life, replacing it is the most reliable fix. The ASUS RT-AX88U Pro is a strong upgrade choice — it supports automatic firmware updates, has a strong security track record, and runs AiProtection (Trend Micro) for real-time threat blocking.
Frequently Asked Questions: Router Hacking
How do I know for sure if my router has been hacked? The most reliable indicators are DNS settings you didn’t configure, unknown devices on your network, and being locked out of your router admin panel. If two or more of these apply, assume your router has been hacked and act immediately with a factory reset followed by a firmware update.
Can a router be hacked through WiFi? Yes. A weak WiFi password allows an attacker within range to join your network. Once on your local network, they can attempt to access the router admin panel using default or common credentials. Using WPA3 and a strong, unique passphrase significantly reduces this risk.
Does factory resetting a router remove a hack? In most cases, yes. A factory reset wipes all configuration changes, backdoor accounts, and altered DNS settings. However, advanced persistent firmware implants (like VPNFilter malware) can survive a factory reset. For these, you need to flash the router with a fresh firmware image downloaded directly from the manufacturer’s official site.
How long can a router stay hacked before you notice? Potentially years. The 360,000-device botnet referenced in this guide operated undetected for 16 years. Most compromised routers show no obvious symptoms — attackers deliberately stay quiet to preserve long-term access. This is exactly why quarterly security checks matter even when nothing seems wrong.
What’s the first thing I should check if I suspect my router has been hacked? Check your DNS settings first. Log into your admin panel, navigate to WAN or Internet settings, and verify the Primary and Secondary DNS servers. Any unfamiliar IP addresses — ones you didn’t set and that don’t belong to your ISP or a known public DNS provider — are the clearest sign of a router hack in progress.
The FCC router ban is pushing many users to upgrade, which is a good time to audit your security.
For secure remote access, consider WireGuard vs Tailscale instead of exposing your router directly.